Article
9 min read
How to Scale Endpoint Security Without Hiring Additional Engineers
IT & device management

Author
Dr Kristine Lennie
Last Update
March 31, 2026

Table of Contents
What does scalable endpoint security actually look like?
1. Connect HR events directly to device security
2. Enforce Security Baselines That Actually Work
3. Consolidate endpoint security tools into a unified control plane
4. Automate triage, containment, and remediation
5. Integrate endpoint security into developer workflows
6. Measure Endpoint Security Outcomes With Clear Metrics
Streamline endpoint security across your global workforce with Deel IT
FAQs
Here's the traditional scaling playbook: More devices = more security engineers.
Here's the problem: It doesn't scale. And it's expensive.
Every new hire brings a new endpoint. Every role change requires permission updates. Every departure creates a security gap. Most companies solve this by throwing headcount at the problem—hiring more analysts, more IT admins, more security engineers.
There's a better way: automation that actually works.
What does scalable endpoint security actually look like?
A scalable endpoint security model isn't about doing more of the same—it's about working differently. It's an automation-first framework that:
- Connects HR lifecycle events (joiner, mover, leaver) directly to identity and device controls
- Enforces standardized security baselines across Windows, macOS, Linux, iOS, and Android
- Deploys EDR/XDR agents automatically, no manual installation required
- Automates triage, containment, and remediation so analysts handle exceptions, not routine alerts
- Measures what matters through coverage rates and remediation speed
Instead of scaling your team as your device count grows, you scale automation coverage.
1. Connect HR events directly to device security
Endpoint security starts the moment someone joins your company. But when HR systems and device management run in silos, gaps appear in the process. New hires wait days for access while their unmanaged devices connect to corporate networks. Role changes mean temporary over-provisioning ("we'll remove the old access next week"). And terminations average 8-24 hours between HR recording the exit and IT revoking access—an unacceptable window for someone with access to customer data or production systems.
Here is how automation can streamline employee lifecycle security:
- Role-based policy assignment: Access to systems should map to the employee's role in your HRIS. When someone moves from Engineering to Sales, their device policies, application access, and network permissions should update automatically.
- Instant offboarding: When HR records a termination, the workflow should trigger account revocation, device lock, and remote wipe without IT intervention. Waiting for IT to manually execute these steps creates unnecessary risk.
How to implement this: Most MDMs don't connect to HR systems directly. You'll need middleware or custom integrations between your HRIS (Workday, BambooHR, etc.) and your MDM. This typically requires:
- API connections between systems
- Webhook triggers for status changes
- Identity provider as the coordination layer (Azure AD/Okta)
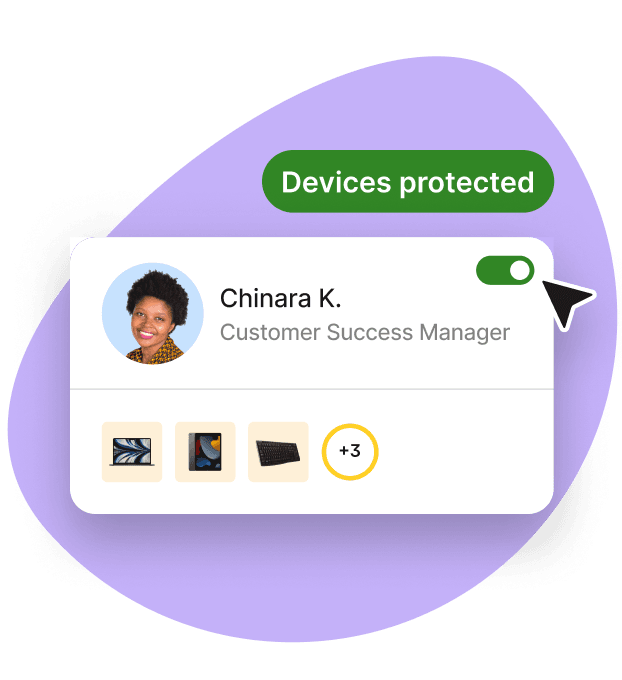
Deel IT simplifies this process by including both HR and MDM in one platform. When someone is hired in Deel, their device auto-enrolls. When they leave, remote wipe and access revocation happen automatically. The integration is built in rather than something you configure.
With Deel IT, HR events from Deel's global platform trigger device and identity controls automatically:
- New hire? Device auto-enrolls through Apple Business Manager, Windows Autopilot, or Android Enterprise before first login
- Role change? Policy assignments and conditional access rules update immediately
- Someone leaving? Device locks, data wipes, and account deactivation happen on their last day—not whenever someone remembers to file a ticket
This means encryption is enforced from day one. Firewalls and logging are on by default. EDR agents deploy automatically. Access to SaaS and production systems requires a compliant device—no exceptions.
Endpoint Protection
Learn about these 5 ways to reduce IT costs in 2026.
2. Enforce Security Baselines That Actually Work
You can't scale what isn't standardized.
Your security posture shouldn't depend on which IT admin provisioned which device. CIS-aligned baselines need to be versioned, applied consistently, and enforced across every OS you support.
The baseline should handle the fundamentals automatically:
- Disk encryption with escrowed recovery keys
- Host-based firewalls are enabled by default
- Screen lock and idle timeout policies
- Patch SLOs that actually get met
- Logging and telemetry standards
- Minimum OS version enforcement
What needs approval: High-risk changes like new authentication models, cross-region data transfers, kernel-level drivers, or sensitive third-party integrations.
What doesn't: Everything else.
This guardrail model keeps you secure without creating bureaucratic overhead. It also ensures a developer in São Paulo and an executive in Singapore have the same baseline security—without manual intervention.
Resources to support your global fleet management
Managing laptops and devices can be complex. These resources help streamline deployment, security, and recovery for a distributed workforce:
- Standardize laptop security: Use our Free IT Policy Template to help you define and enforce a consistent policy across your organization.
- Simplify onboarding and offboarding with this Onboarding & Offboarding Guide for Distributed Teams.
- Plan for growth: Use the IT Strategy Toolkit: 2026 Guide to identify automation opportunities and create a roadmap for building scalable operations.
- Formalize global provisioning: Download this Equipment Provisioning Policy Template to help you standardize device delivery, tracking, and recovery worldwide.
3. Consolidate endpoint security tools into a unified control plane
Tool sprawl increases operational complexity.
Most endpoint security vendors focus on a single layer of the stack: EDR/XDR platforms handle detection and response, UEM tools manage configuration and patching, and identity providers enforce authentication and conditional access. Each category solves a real problem. But they assume someone else will connect them.
As organizations scale, that “someone else” becomes internal engineering time. Integration work accumulates. Policy drifts across tools. Reporting fragments. Manual coordination increases.
A scalable endpoint security model replaces fragmentation with a unified control plane: one that centralizes device inventory, configuration management, patching, detection and response, policy enforcement, identity integration, and telemetry routing into a single operational layer.
The impact of consolidation is measurable:
- A single source of truth for device posture
- Consistent policy enforcement across operating systems
- Fewer duplicate alerts and manual handoffs
- Standardized patch windows and maintenance cycles
- Centralized reporting for audits and compliance
For IT managers, this reduces context switching and operational drag. For HR leaders, it ensures global consistency as hiring expands across regions.
When endpoint operations run through a unified control plane, scaling the fleet no longer requires scaling the team.
4. Automate triage, containment, and remediation
As endpoint coverage increases, alert volume rises with it. Even with a unified control plane, manual triage creates a bottleneck. Every alert routed to a human queue increases response latency.
A scalable endpoint security model minimizes analyst intervention by automating predictable response actions.
Modern EDR/XDR platforms support policy-driven workflows that automatically execute when alerts meet defined risk thresholds. Instead of waiting for manual review, the system can:
- Isolate infected hosts from the network
- Terminate malicious processes
- Quarantine suspicious files
- Reset compromised credentials
- Deploy urgent patches
- Roll back ransomware changes
Automation handles the high-frequency, well-understood incidents. Analysts focus on anomalies and novel threats.
Contextual enrichment further improves efficiency. Alerts weighted by asset criticality, executive ownership, or production access are prioritized automatically, reducing noise and improving containment speed where it matters most.
The result is not just lower MTTR—it is predictable containment at scale.
That predictability is what allows security teams to absorb fleet growth without expanding staffing.
5. Integrate endpoint security into developer workflows
Security bottlenecks occur when controls are detached from operational workflows.
A scalable model integrates endpoint compliance checks into:
- CI/CD pipelines
- Pull requests
- Configuration repositories
- ITSM systems (e.g., Jira, ServiceNow)
- Conditional access policies
Policy-as-code validation can prevent non-compliant configuration updates before rollout. Automated ticket routing ensures remediation tasks are assigned with clear ownership and deadlines.
This approach reduces queue buildup and improves resolution speed.
6. Measure Endpoint Security Outcomes With Clear Metrics
Endpoint security at scale requires measurable performance indicators.
The following metrics provide visibility into both coverage and operational quality:
| Metric | What it shows | Desired trend |
|---|---|---|
| % endpoints with policy coverage | Enforcement consistency across the fleet | Stable above 98% |
| Mean Time to Remediate (MTTR) | Remediation efficiency | Decreasing over time |
| Patch latency (critical) | Exposure window duration | ≤48 hours |
| High-severity alerts reopened | Fix quality | Approaching zero |
| Exceptions open >30 days | Accumulated risk debt | Steadily declining |
When these metrics improve while headcount remains constant, automation is functioning effectively.
Regular reviews between IT, security, and HR ensure service levels remain aligned with workforce growth.
Streamline endpoint security across your global workforce with Deel IT
Endpoint security does not need to be stitched together across vendors, regions, and disconnected systems.
Deel IT brings device provisioning, identity orchestration, security enforcement, automated remediation, support, and recovery together in one global platform — so IT teams can manage the full endpoint lifecycle consistently, wherever they hire.
Why organizations choose Deel IT to scale endpoint security:
- Lifecycle-driven automation: HR changes automatically trigger device, identity, and security controls
- Zero-touch global provisioning: Secure devices are delivered and enrolled with hardened baselines before first login
- Unified visibility: Track coverage, patch latency, MTTR, and exceptions in one place
- Cross-platform consistency: Manage Windows, macOS, Linux, iOS, and Android under a standardized framework
- Global by default: Deliver, manage, support, and recover devices in 130+ countries
- 24/7 IT support with integrated workflows: Reduce operational load without building regional IT teams
With Deel IT, endpoint security operates as a connected, automated lifecycle — not a collection of tools.
As your workforce grows, your security posture scales with it.
Book a demo with Deel IT to see how.
Deel IT
FAQs
How can automation reduce the need for additional endpoint security staff?
Automation—delivered by Deel IT or your internal team—handles high-volume tasks, such as device enrollment, patching, isolation, and alert triage, so a lean team can manage more endpoints with consistent outcomes. Deel IT connects HR events to zero-touch provisioning, enforces patch rings and maintenance windows, and runs EDR playbooks that isolate hosts and roll back changes without manual intervention.
What role do centralized policies play in scaling endpoint security?
Centralized policies—managed by Deel IT or your security team—enforce uniform controls across every device, cutting manual configuration and error rates as the fleet grows. Deel IT maintains versioned baselines per OS, pushes updates automatically, and verifies compliance continuously, gating access to sensitive apps when a device falls out of policy.
How can integration with developer tools improve security efficiency?
Embedding checks in CI/CD and pull requests surfaces issues earlier, and routes fixes to the owners, reducing bottlenecks and rework; Deel IT can integrate these checks into your workflows. For example, policy-as-code tests fail builds that would disable encryption or uninstall EDR, while auto-generated Jira/ServiceNow tickets include remediation steps and SLAs.
What metrics should be tracked to measure endpoint security effectiveness?
Monitor incident response time, policy coverage, alert volume and severity, patch latency, and recurrence to spot gaps and tune automation. Deel IT provides dashboards and monthly reports, highlights drift, and proposes rule or policy changes to keep metrics trending in the right direction.
How does adopting zero-trust principles support scalable endpoint protection?
Continuous verification and least-privilege access apply consistent controls to every device and user, making expansion safer without adding headcount. Deel IT feeds device compliance into conditional access policies so only healthy, encrypted, and EDR-protected devices can reach sensitive systems, all enforced automatically at scale.

Dr Kristine Lennie holds a PhD in Mathematical Biology and loves learning, research and content creation. She had written academic, creative and industry-related content and enjoys exploring new topics and ideas. She is passionate about helping create a truly global workforce, where employers and employees are not limited by borders to achieve success.